Before you begin
We're rolling out a new, more intuitive product experience. If the screen shown here doesn’t match your product interface, select help for your current experience.
Before you begin
We're rolling out a new, more intuitive product experience. If the screen shown here doesn’t match your product interface, select help for your current experience.
PDFs have evolved from static pages to complex documents with features such as interactive forms, multimedia content, scripting, and other capabilities. These features leave PDFs vulnerable to malicious scripts or actions that can damage your computer or steal data. Enhanced security lets you protect your computer against these threats by blocking or selectively permitting actions for trusted locations and files.
When enhanced security is enabled and a PDF tries to complete a restricted action from an untrusted location or file, a security warning appears. The type of warning depends on the action and your version of Acrobat or Acrobat Reader. (See Security warnings.)
For technical details about enhanced security, primarily for administrators, see the Acrobat Application Security Guide.
Adobe recommends that you enable sandbox protection if it isn't already enabled.
On macOS, this capability is being rolled out in phases and may not be available to all users yet.
Select Acrobat > Preferences > Security (Enhanced).
Select Enable Protected Mode at startup and then select OK.
Confirm the changes by selecting Yes in the dialog box that appears.
Restart Acrobat.
Disable the sandbox protection only when required for certain workflows, as it provides essential security measures.
Acrobat and Acrobat Reader enable enhanced security by default. Adobe recommends that you enable enhanced security if it isn't already enabled, and that you bypass restrictions only for trusted content.
With enhanced security enabled, only the files, folders, and locations that have been trusted are exempt from enhanced security’s restrictions. You can specify trusted locations and files in several ways, depending on the action the PDF is attempting to complete.
Use the privileged locations feature in the Enhanced Security panel to trust files, folders, and host domains (root URLs).
Configure Internet access using the Trust Manager. (See URL settings.)
For certified PDFs, trust the signer’s certificate for privileged network operations, such as networking, printing, and file access. (See Set the trust level of a certificate.)
Control cross-domain access using a server-based policy file. (See the Cross Domain Security section in the Acrobat Application Security Guide.)
Enhanced security provides a way to specify locations for trusted content. These privileged locations can be single files, folders, or host domains (root URLs). Content that resides in a privileged location is trusted. For example, enhanced security normally blocks PDFs from loading data from unknown websites. If you add the data’s origin (its host domain) to your list of privileged locations, Acrobat and Acrobat Reader allow loading of the data. For details, see the Enhanced Security section in Acrobat Application Security Guide.
Select Enable Enhanced Security.
Specify a list of locations under Privileged Locations, and then select OK.
To trust any sites you already trust in Internet Explorer, select Automatically Trust Sites From My Win OS Security Zones.
To add only one or two PDFs from a location, click Add File.
To create a trusted folder for multiple PDFs, click Add Folder Path or Add Host.
To allow data to load from a website, enter the name of the root URL. For example, enter www.adobe.com, but not www.adobe.com/products. To trust files from secure connections only, select Secure Connections Only (https:).
The Automatically Trust Sites From My Win OS Security Zones setting is applicable when Protected View is set to Files From Potentially Unsafe Locations.
If you set Protected View to All Files, trusted sites will open in protected view, by default, unless you add the sites to the Privileged Locations list.
Enhanced security prevents a PDF in one host domain from communicating with another domain. This action prevents a PDF from getting malicious data from an untrusted source. When a PDF attempts cross-domain access, Acrobat and Acrobat Reader automatically attempt to load a policy file from that domain. If the domain of the document that is attempting to access the data is included in the policy file, then the data is automatically accessible.
For more details, see the Acrobat Application Security Guide.
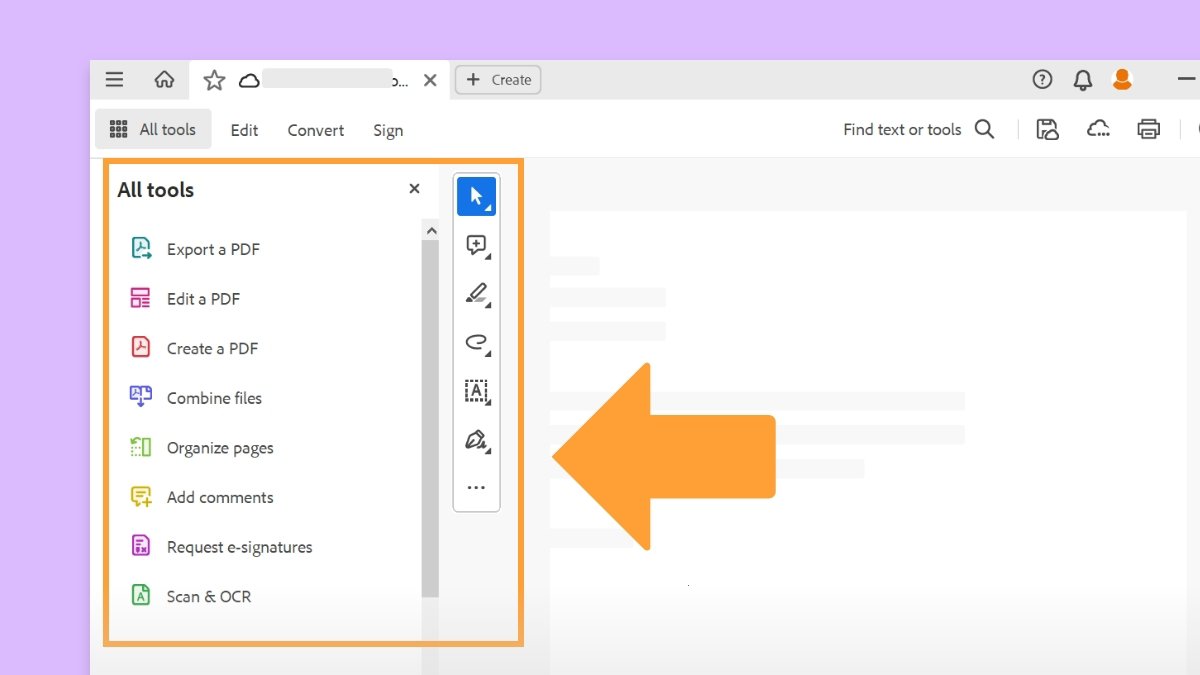
Work smarter with Acrobat on your desktop
Create, edit, and organize PDFs with powerful tools that help you stay productive anywhere.