Update the security settings on your Single Sign On (SSO) server
If you have configured your Adobe Sign account to use SSO login, and are using the Adobe Sign iOS mobile app, please check to see if your SSO server supports Apple’s App Transport Security (ATS) security requirements. Update your servers to support Apple’s ATS requirements before December 1, 2016 in order to continue your SSO access to the Adobe Sign iOS application.
Background
In iOS9, Apple introduced a new security feature called App Transport Security (ATS) that requires servers to support TLS (Transport Layer Security) version 1.2 and Forward Secrecy. This feature is described in the iOS9 release notes in the section titled “App Transport Security” -
https://developer.apple.com/library/ios/releasenotes/General/WhatsNewIniOS/Articles/iOS9.html
When an iOS9 app attempts to communicate with servers that do not meet these requirements for login via Single Sign On (SSO), an error is returned and communication fails.
As a short term remediation, we implemented a temporary solution in the April 2016 release of the Adobe Sign iOS app (v3.3.2) that used the newer standards with servers supporting TLS1.2, but also worked with older servers so that you could continue to login and use the mobile application.
This interim solution provided the opportunity to update any servers to support the newer, more secure standards. However, at WWDC 2016 in June, Apple announced the enforcement of App Transport Security (ATS) for all mobile applications submitted to the App Store by the end of 2016. What this means is that any mobile application that does not support ATS or tries to bypass the ATS requirements, will be rejected by App Store after January 1, 2017. The Adobe Sign iOS app will be removing the short-term mediation that allowed for exceptions by December 1, 2016.
Action Required
Update your servers to support the App Transport Security requirements before December 1, 2016 in order to continue your SSO access to the Adobe Sign iOS application.
Testing ATS Connection Capability
Here are two ways to check if the server is compliant with ATS:
Method 1:
SSL labs (which has become the industry standard for measuring security of TLS configuration) has a check for ATS compliance.
Steps:
- Go to this URL: https://www.ssllabs.com/ssltest/analyze.html
- Enter the URL of an SSO endpoint you want to verify for ATS compliance. (You can find yours in the Adobe Sign web client by going to the Account Tab, then Account Settings, then SAML Settings. To be thorough, check all three of the URLs in the Identity Provider (IdP) Configuration.)
- Press Submit
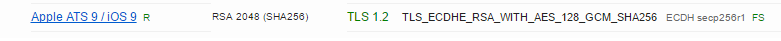
- Once the results are ready, check “Apple ATS 9 / iOS 9” option in the “Handshake Simulation” option. If it is green, it means that your server supports ATS requirements.
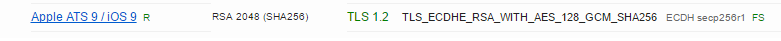
5. If your server does not support ATS requirements, then you will see a red error message similar to the error below:


Method 2: (Using a Mac OS machine)
If you are using MAC OS X 10.11 "El Capitan", you can also use the nscurl command.
In the MAC Terminal, type:
/usr/bin/nscurl--ats-diagnostics <url to test>
If the url is ATS compatible, you will see:
Default ATS Secure Connection
---
ATS Default Connection
Result: PASS
---
Updating your server
Please contact your IT department to update security settings on your SSO server to support TLS v1.2 & Forward Secrecy for continued use of the Adobe Sign iOS mobile app. The information needed is available in the section titled “NSAppTransportSecurity” in the following URL: